Fast16: Cyberweapon that predates Stuxnet by five years
A previously unknown cyberweapon named fast16, active since 2005 and undetected for 21 years, sabotaged scientific and engineering simulations by subtly altering floating-point calculations without leaving traces on disk. Unlike Stuxnet, which caused physical destruction, fast16 corrupted data in high-precision software used for nuclear, structural, and environmental modeling, making results appear valid while being fundamentally flawed. Researchers linked it to the NSA's Equation Group through a clue in the 2017 ShadowBrokers leak, and it evaded detection for years despite being uploaded to VirusTotal in 2016. The malware used a sophisticated three-layer architecture, including a Lua scripting engine, and targeted specific compilers and applications like LS-DYNA, PKPM, and MOHID.
Full article excerpt tap to expand
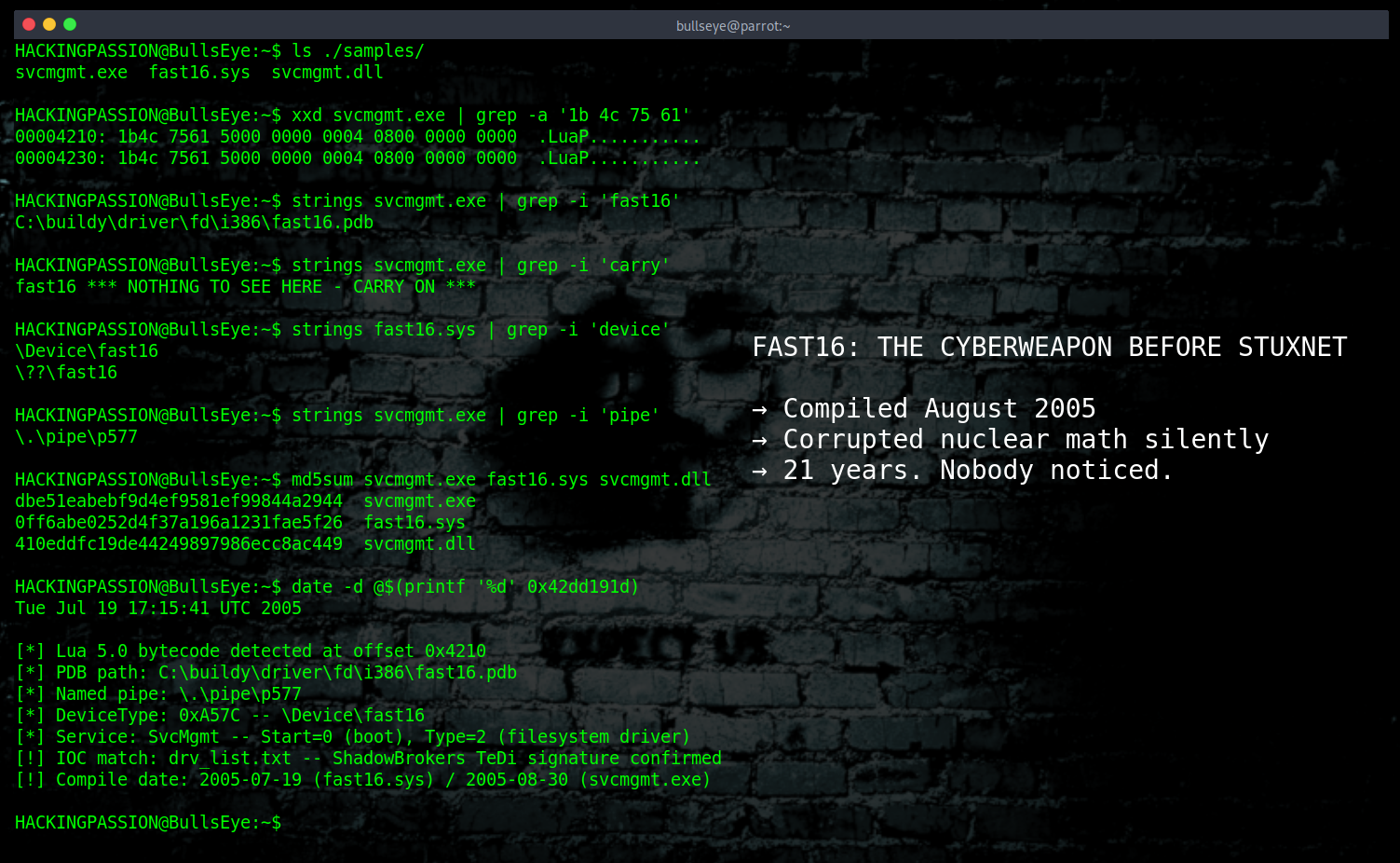
Fast16: The Cyberweapon That Predates Stuxnet by Five Years Bulls Eye included in Security News 2026-04-26 2071 words 10 minutes Want to learn ethical hacking? I built a complete course. Have a look!Learn penetration testing, web exploitation, network security, and the hacker mindset:→ Master ethical hacking hands-onHacking is not a hobby but a way of life! Contents For 21 years, a cyberweapon called fast16 sat completely undetected. This one did not destroy machines or blow things up. It corrupted the math. Scientists running nuclear and engineering simulations got output that looked completely normal, every number added up, every result made sense, and all of it was deliberately wrong. It surfaced last week. It predates Stuxnet by five years.SentinelOne researchers Vitaly Kamluk and Juan Andrés Guerrero-Saade presented the full analysis of fast16 at Black Hat Asia last week. Fast16’s core binary has a compilation timestamp of August 30, 2005. Stuxnet’s C&C infrastructure was set up in November that same year.Most people in security know Stuxnet as the worm that destroyed centrifuges at Iran’s Natanz nuclear facility around 2010, by pushing them past their mechanical limits while lying to the monitoring software about what was happening. It was the first known cyberweapon designed to cause physical destruction, and for years it was considered the starting point of this whole era. Fast16 was there first, and for a long time it was the only one.Kamluk started with a hunch. He had noticed that the most sophisticated state-sponsored malware families he knew about all shared one technical habit: each one had a small scripting engine built in called Lua. Lua works like a remote control for malware, it lets operators change what the implant does while it is already running on a target machine, without needing to send a completely new file. He wanted to know if something older had done the same thing first, and went looking through old collections.What he found was a file on VirusTotal called svcmgmt.exe, uploaded in October 2016 and flagged by almost nobody. It looked like a boring Windows service wrapper from the XP era. But inside it was an embedded Lua 5.0 virtual machine, encrypted bytecode, and a path pointing to a kernel driver called fast16.sys. That makes fast16 the earliest known Windows malware to embed a Lua engine, predating the next known example by three full years.One more thing confirms the timeline. Fast16 only runs on single-core processors, built at a time when most machines were still running on a single core and multi-core was just beginning to arrive on the market.The framework runs in three layers. The outer layer is svcmgmt.exe, a carrier that behaves differently depending on how it is launched. Pass it -p and it spreads across the network. Pass it -i and it installs itself as a Windows service and runs the embedded payload. Pass it -r and it runs the payload without installing. Inside the carrier are three things stored in encrypted form: the Lua bytecode that handles the operational logic, a DLL that hooks into Windows’ dial-up and VPN connection system, and fast16.sys itself. That DLL is worth a closer look. Every time a machine connects to a remote network, it writes the connection details to a named pipe that operators can read. So while fast16.sys was corrupting calculations on disk, the DLL was quietly mapping out which machines were connecting to which networks, giving operators a live picture of the…
This excerpt is published under fair use for community discussion. Read the full article at HackingPassion.com : root@HackingPassion.com-[~].





